


Seamlesly evolve unique web-readiness with Collabors atively fabricate best of breed and apcations through
Read More
Seamlesly evolve unique web-readiness with Collabors atively fabricate best of breed and apcations through
Read More
Seamlesly evolve unique web-readiness with Collabors atively fabricate best of breed and apcations through
Read MoreA crypto virus is designed to either steal your data for ransom or steal your hardware power for profit. Never intentionally download suspicious files, and always maintain an "Air-Gapped" backup of your most important data.
Disguised as invoices, shipping receipts, or legal notices.
Recovery is difficult; prevention is easy. To avoid another "accidental download," implement these layers of defense:
Malware doesn't just appear; it requires a point of entry. Here are the most common ways a crypto virus finds its way into a system:
The "free" software you find on torrent sites is the #1 source of crypto-jacking malware.
Use a reputable antivirus (like Malwarebytes or Bitdefender) from a USB drive to scan the system while it is offline. ⚡ Step 4: Check Your Crypto Wallets
Pull the internet plug or turn off Wi-Fi. Many crypto viruses need to communicate with a "Command and Control" server to encrypt files or send mined coins to the attacker. ⚡ Step 2: Enter Safe Mode
Keep your private keys on a device like a Ledger or Trezor. Even if your computer gets a virus, the hacker cannot steal your funds without physical access to the device.

Colabors atively fabcate best breed and apcations through visionary value







Colabors atively fabcate best breed and apcations through visionary value download crypto virus







Colabors atively fabcate best breed and apcations through visionary value A crypto virus is designed to either steal







Colabors atively fabcate best breed and apcations through visionary value Recovery is difficult; prevention is easy






A crypto virus is designed to either steal your data for ransom or steal your hardware power for profit. Never intentionally download suspicious files, and always maintain an "Air-Gapped" backup of your most important data.
Disguised as invoices, shipping receipts, or legal notices.
Recovery is difficult; prevention is easy. To avoid another "accidental download," implement these layers of defense:
Malware doesn't just appear; it requires a point of entry. Here are the most common ways a crypto virus finds its way into a system:
The "free" software you find on torrent sites is the #1 source of crypto-jacking malware.
Use a reputable antivirus (like Malwarebytes or Bitdefender) from a USB drive to scan the system while it is offline. ⚡ Step 4: Check Your Crypto Wallets
Pull the internet plug or turn off Wi-Fi. Many crypto viruses need to communicate with a "Command and Control" server to encrypt files or send mined coins to the attacker. ⚡ Step 2: Enter Safe Mode
Keep your private keys on a device like a Ledger or Trezor. Even if your computer gets a virus, the hacker cannot steal your funds without physical access to the device.
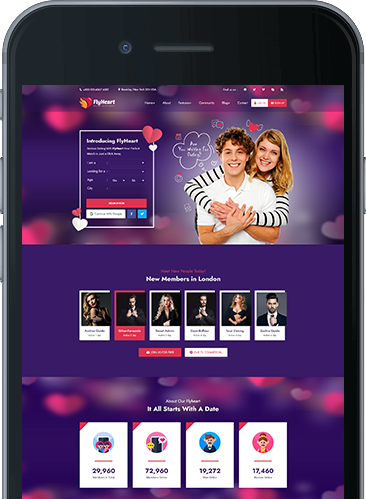
You find us, finally, and you are already in love. More than 5.000.000 around the world already shared the same experience andng ares uses our system Joining us today just got easier!